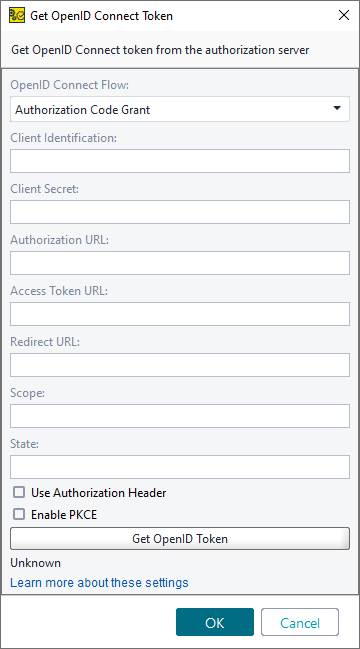
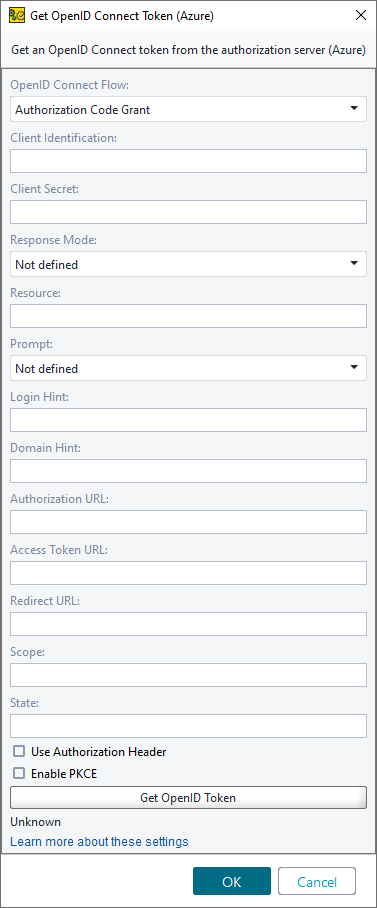
OpenID Authorization Code Grant
The OpenID Connect ID Token is retrieved in almost the same way as an OAuth 2.0 access token when you use Implicit and Authorization Code grants.
When the Authorization Code grant connect flow is used, the resource owner first provides access, then an authorization code is sent to the client through a browser redirect. The client then uses it to get an access token. Optionally, a refresh token is also sent.
Option | Description |
|---|---|
OpenID Connect Flow | The OpenID Connect method to use. |
Client Identification | An alphanumeric string used to identify the client. |
Client Secret | The secret string the client will use. |
Response Mode | (For Azure only) Specifies how the authorization server sends the access token. Available options:
|
Resource | (For Azure only) The App ID URI of the web service. |
Prompt | (For Azure only) Specifies if the authentication server prompts the user to log in or consent, even if they are logged in. Possible values:
|
Login Hint | (For Azure only) The string is displayed as a login hint in the sign-in form. |
Domain Hint | (For Azure only) Specifies the domain the user should use to sign in. |
Authorization URL | The authorization server URL. |
Access Token URL | The URL to use to get an access token. |
Redirect URL | The URL you will be redirected to after successful authorization. |
Audience | Identifies the intended recipient of the token. Some authorization servers require this value to specify the target API or resource that accepts the token. |
Additional Parameters | Custom name–value pairs to include in the OpenID Connect token request. ReadyAPI appends these parameters to the request body and supports property expansion for their values. |
Scope | The full scope string defining the requested permissions. |
State | (For Azure only) The value included in the request that is also added to the token response. Usually, it is used to provide a randomly generated string to prevent a cross-site request forgery attack. |
Use Authorization Header | Select to send client credentials in the request header. Otherwise, the credentials are sent in the request body. |
Enable PKCE | Enables Proof Key for Code Exchange (PKCE) for the authorization request. PKCE adds a security layer by preventing authorization code interception and is commonly required for public clients and OpenID Connect flows. |
Get OpenID Token | Click this button to retrieve the OpenID Connect token. |
Automation | Opens the Automated Token Profile editor. |